
The great Google Ads heist
An ongoing malvertising campaign steals Google advertiser accounts via fraudulent ads for Google Ads itself.
As a security researcher with extensive experience uncovering client-side web threats such as malvertising, skimming or drive-by exploits, I have built tools to identify compromised websites, and collaborated with industry partners and law enforcement to take down threat actors.
In addition to publishing original research, I also share my discoveries with media outlets and occasionally present at security conferences.

An ongoing malvertising campaign steals Google advertiser accounts via fraudulent ads for Google Ads itself.

The #opentowork hashtag may attract the wrong crowd as criminals target LinkedIn users to steal personal information, or scam them.

While Magecart threat actors usually pick domain names after third-party libraries, or Google Analytics, in this case they went with a crypto-inspired theme which we had not seen before.

Documenting how threat actors used targeted traffic-filtering coupled with steganography to create the most elaborate browser locker traffic scheme to date.
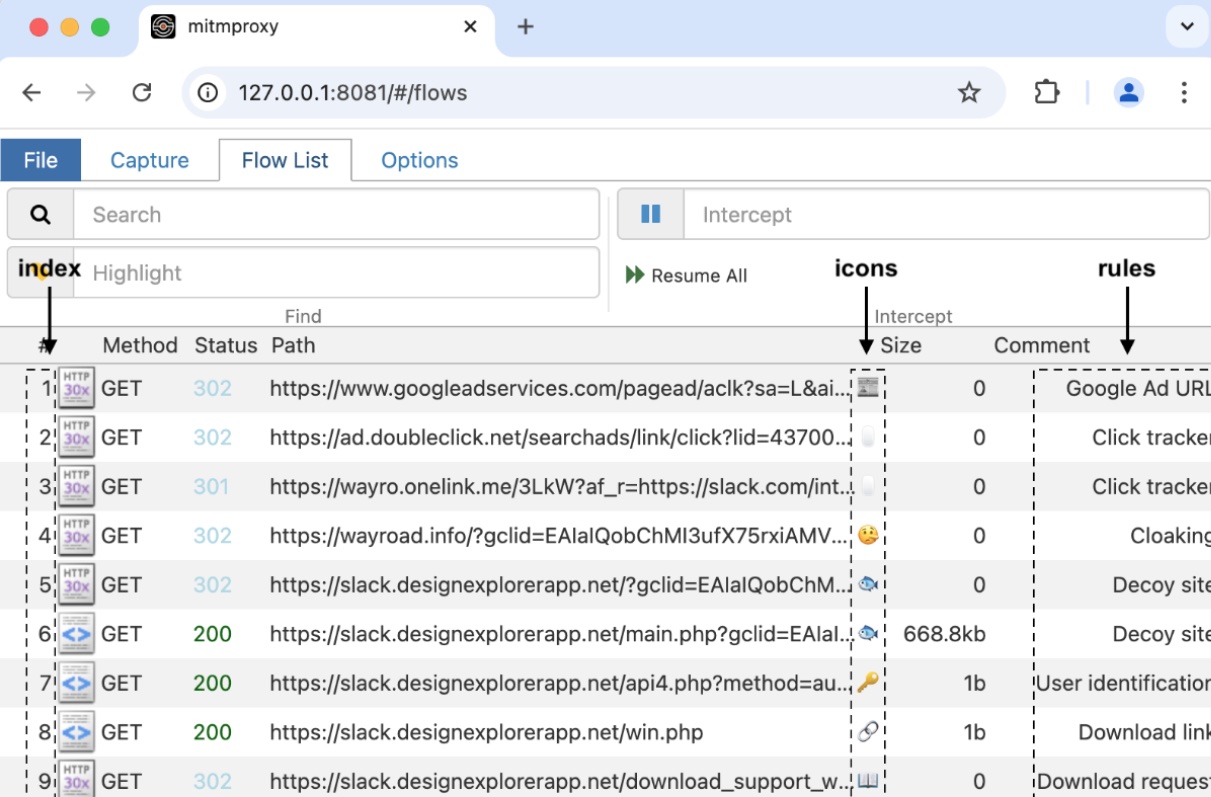
An addon for mitmproxy designed for security researchers interested in capturing and analyzing web-based threats. Language: Python
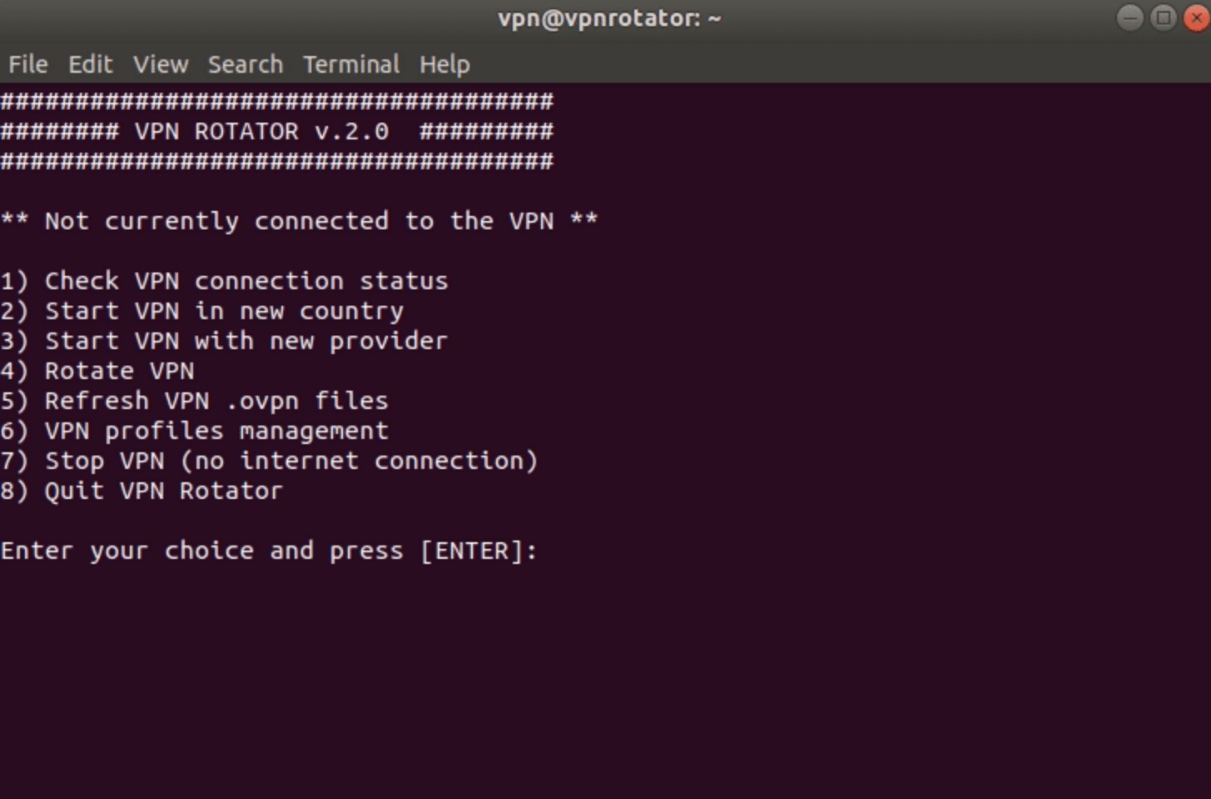
Debian framework to safely replay malicious traffic from different geolocations. Language: Bash
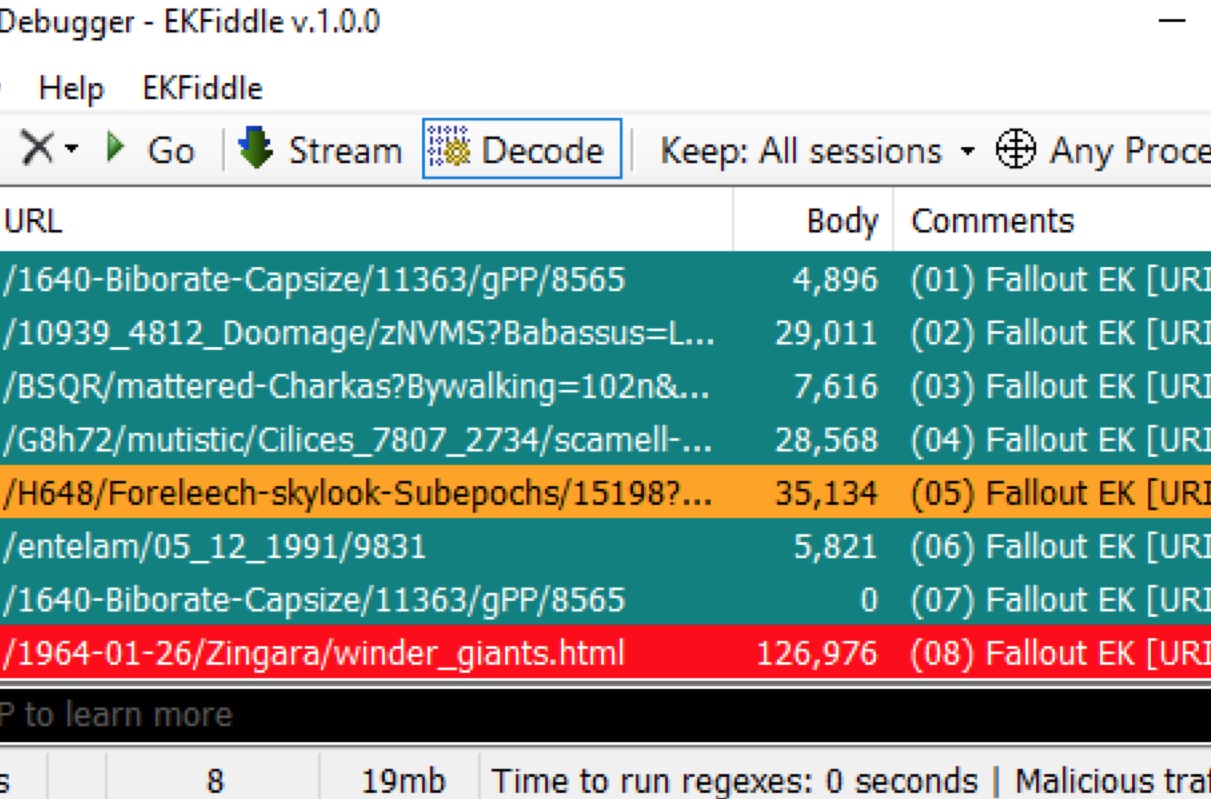
My first project with the Fiddler web debugger used for years to analyze malicious web traffic. Language: C#